Custom Software & AI Solutions
Zenith Point Innovations designs and delivers end-to-end solutions across Windows desktop applications, 3D computer vision, and AI that adds measurable business value. Systems are built to be fast, secure, and production-ready, with practical deployment options that fit real-world use.
Systems We Design and Deliver
WHAT WE DO
Windows Desktop Applications
Secure, high-performance applications with polished user experiences and strong system integration.
3D Computer Vision and Spatial Systems
Pipelines for object detection, pose estimation, and spatial understanding, including point cloud processing and real-world environment analysis.
Predictive AI
Models for forecasting, anomaly detection, and decision automation, turning data into reliable, actionable insight
Generative AI Systems
Custom AI systems that automate content, summarize documents, and use internal knowledge securely.







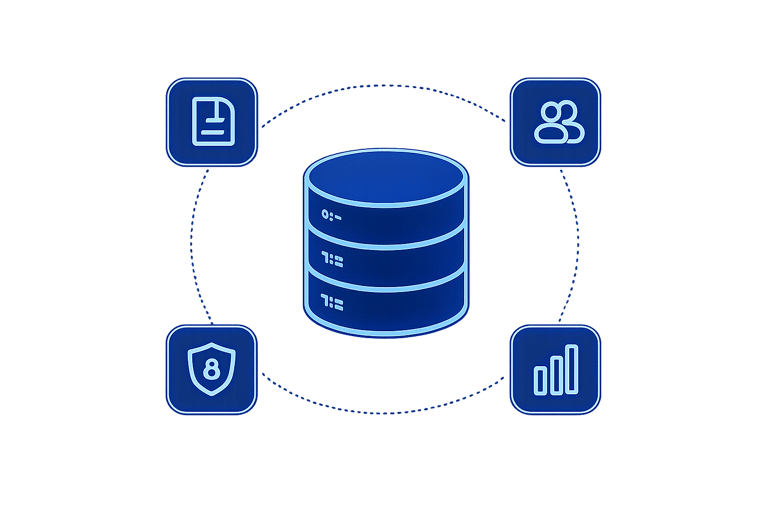
01 | Working with Your Data
Businesses rely on valuable internal information such as contracts, product data, customer records, and operational knowledge.
To be effective, AI systems must access this information in a way that is accurate, up to date, and secure. Large language models are powerful tools, but they are not designed to act as private data storage systems. Sending sensitive data into unmanaged environments can create risk.
Systems are built to keep data controlled and protected while still making it usable for real tasks.
02 | How the System Learns Your Business and Adapts
03 | Deployment, Security, and Control
Making Your Data Usable, Secure, and Actionable
Our System turns your initial information into accurate, reliable insights so you can make better decitions with confidence
Hybrid Approach
A combination of both methods balances accuracy, performance, and up-to-date information.
Fine-Tuning on Your Data
Models can be trained on internal materials to produce faster, more consistent outputs aligned with business-specific knowledge and tone.
Context by Retrieval
Relevant documents are pulled in real time to generate accurate, context-aware responses with traceable sources.
Systems are deployed either on controlled local hardware for maximum data ownership and low latency, or within a secure private cloud environment with strong access controls.
Security is built in at every level, with restricted system access, encryption in transit and at rest, controlled permissions, and auditable outputs and activity.